The Trusted Employee Syndrome
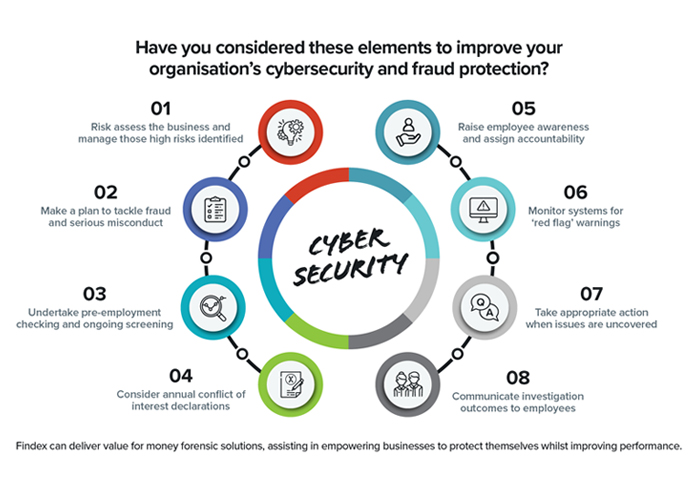
Organisations need to consider the following when it comes to cyber security:
The employee
He had it all in front of him. At 27, he was a management accountant in a successful company, happily married with a two-year-old and another on the way.
But his interest in American sports – and more importantly, gambling on them – was too much. When he was in a hole after maxing out his credits cards and mortgage, he quite literally “borrowed” up to $550,000 from his employer to fund his gambling habit. And he was caught – quite by accident.
He used a variety of methods to extract cash from the business including the use of fictitious computer-generated invoicing, abuse of online payment processes relating to a divested entity and the manipulation of accounting balances to cover his trail.
The ease at which this employee committed the fraud was alarming when you consider the entity was supposed to be dormant and yet it was still linked to the Group’s main trading account via a bank sweeping facility.
The employee was also the Treasurer of his local sporting club and was using their account to launder the proceeds. The fraud was only discovered when a diligent employee of the club noticed an unusually large balance in the account when he deposited the weekly bar takings.
In many ways, the fraud was not overly surprising. The ability to disguise the electronic transfer of funds may be reserved to those few with access, but what about the potential exposure of confidential information or proprietary documents over the internet which is at the fingertips of almost everyone in your organisation.
The employer
It should be the responsibility of everyone in the company to assess what critical assets are at risk of internal theft or fraud. Thankfully, there are several options available to minimise fraud and ‘abuse of trust’ practices taking root in the office. It is good practice to develop a sound ethics policy linked to a Code of Conduct and to provide clear reporting guidelines in the event someone does the wrong thing.
Importantly, employers need to communicate their expectations and should provide ongoing training to all employees that ensures adequate understanding, compliance and clear escalation guidelines.
Many organisations have well established risk management strategies in place. However, there’s been a slew of new legislation governing how organisations manage and secure their confidential information.
Australian regulations
With Australia’s Notifiable Data Breaches Scheme and the European Union’s General Data Protection Regulations now in place, as well as Consumer Data Right legislation looming, Australian organisations can no longer be complacent and need to have much tighter control over their confidential customer information regardless of whether they have an online presence.
There are now significant penalties for those who choose to run the gauntlet in the hope that it never happens to them.
The Office of the Australian Information Commissioner (OAIC) has recently released its second report into notifications under the Notifiable Data Breach scheme. Of the 242 notifications in the last quarter, 142 (59%) related to criminal or malicious conduct, followed by 88 (36%) caused by human error and the remaining 12 (5%) caused by system faults.
The most common human errors were emails sent to the wrong participant with personal information, unintended release of personal information and physical mail sent to the wrong recipient containing personal information.
It is fair to say that reliance is being increasingly placed on operating and system controls to prevent and detect instances of fraud and misconduct in the workplace, particularly in the face of a de-layering of middle management and withdrawal of internal audit and risk management resources.
This trend seems to be abating partly due to recent high profile corporate incidents, both here and overseas, and a tightening of the regulatory noose around those charged with the governance of companies.
Whilst cost management is necessary in the face of increasing pressure on margins, it is advisable to retain corporate security and fraud prevention initiatives to mitigate the risk of fraud and misconduct occurring.
Those of us who are involved in helping companies get through new requirements, as well as investigating breaches, are too familiar with stories such as that at the top of this piece. ‘Red flags’ were obvious.
There was no management supervision of the employee concerned, and poor segregation of duties; he had access to raising and authorising vendor payments, whilst recording and reporting the same transaction in the accounts. A number of key controls were absent including independent monitoring of movements against provisions and review of intercompany adjustments through the sweep account, not to mention monitoring of employee access to online gambling sites.
Another example...
In another investigation, the Company Secretary of a large publicly listed company decided to take a holiday. While he was away, the company’s bankers telephoned accounting staff expressing concerns about the state of company’s overdraft facility. They were keen to understand likely future collections in order to calculate the repayment of the current overdraft limit which had reached $10 million.
Further internal investigation revealed that over an 18-month period, the Company Secretary had influenced a junior accountant to electronically transfer significant funds to external sources controlled by him for his own personal benefit. These transfers were disguised by an over-statement in debtors and other similar accounting irregularities.
Unfortunately, when an employee has a strong motive to steal, they tend to rationalise their actions as being acceptable. When you combine this with poor internal controls and little likelihood of detection, you have a recipe for financial and reputational disaster.
The number of corporate fraud investigations continues to steadily increase, so greater emphasis needs to be placed on prevention, particularly as it is a lot cheaper to prevent than to investigate.
Business owners and managers need to raise their level of awareness about the techniques used by workplace criminals, in order to better understand their organisation’s vulnerabilities. In doing so, they can strengthen the organisation’s resistance to fraud. The result will hopefully be early detection, efficient investigation (if necessary) and a better more cost-effective outcome for all concerned.
So, in summary, organisations should consider the following:
-
Risk assess the business and manage those high risks identified
-
Make a plan to tackle fraud and serious misconduct
-
Undertake pre-employment checking and ongoing screening
-
Consider annual conflict of interest declarations
-
Raise employee awareness and assign accountability
-
Monitor systems for ‘red flag’ warnings
-
Take appropriate action when issues are uncovered
-
Communicate investigation outcomes to employees.